Whether you need a complete IT security strategy, improvement to metrics to drive your security maturity or a service-based security resource, our security strategy experts and vCISO’s can help.
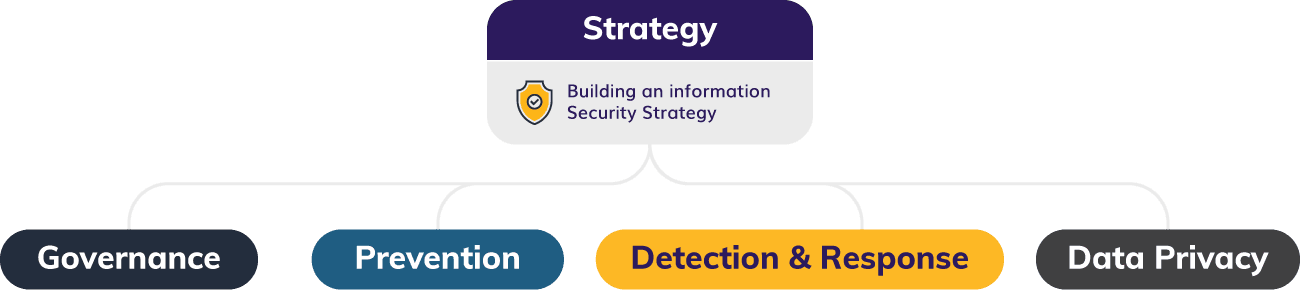
Our holistic approach to strategy includes governance, prevention, detection/response, and data privacy.
Project types include:
- C Suite Advisory
- Cyber Resilience & Attack Recovery
- Risk Management & Migration
- GRC (governance, risk and compliance) Strategy & Utilization
- M&A Security Diligence
- Cyber Liability Insurance
We provide a systematic evaluation of an organization’s cybersecurity policies, procedures and effectiveness.
We help organizations identify and address security gaps, mitigate risks, and ensure compliance with relevant regulations.
Services include:
- Controls Design & Testing
- HITRUST Readiness & Certifications
- SOC Readiness & Reporting
- SOX Testing & IT Audit
GRC provides a holistic approach to an organization’s cybersecurity posture and results in an overall successful cybersecurity program.
Governance establishes policies and procedures, risk is the identification and mitigation of threats to a company’s information assets, and compliance is adherence to relevant laws, regulations, and industry standards.
We can help with:
- Risk Calculation & Quantification
- Regulatory Compliance
- Cyber Benchmark Measurement & Development
- Framework Selection, Adoption, and Implementation
- Compliance Management
Our Penetration Testing team can simulate various kinds of cyber attacks to help identify and exploit vulnerabilities so they can be fixed before they are exploited by real attackers.
For all types of penetration testing, we provide detailed analysis of threats through thorough evaluations using leading tools.
Our penetration testing capabilities include:
- Network Penetration Testing
- Application Security & Penetration Testing
- Social Engineering Testing
- Specialized Penetration Testing
- Open-Source Intelligence Gathering (OSINT)
- Vulnerability Management
Learn More
Effective IAM ensures only authorized users have access to sensitive information and is revoked when no longer needed.
Our experts can help assess your needs, develop an IAM program and roadmap, implement your solution, train your employees, and ultimately monitor your IAM solution.
Project types include:
- Strategy & Policy Definition
- IAM Program Review & Development
- IAM Implementation
- Controls Implementation
- Emerging Technology (BIO, RPA, etc.)
A complete cybersecurity program needs to consider the specific technology deployed to support your business.
Our platform experts consider security paramount and can help with identifying risk, implementing controls, and securing deployments of leading applications.
How we help: